Speak Freely.
Vanish Completely.
Leave No Trace.
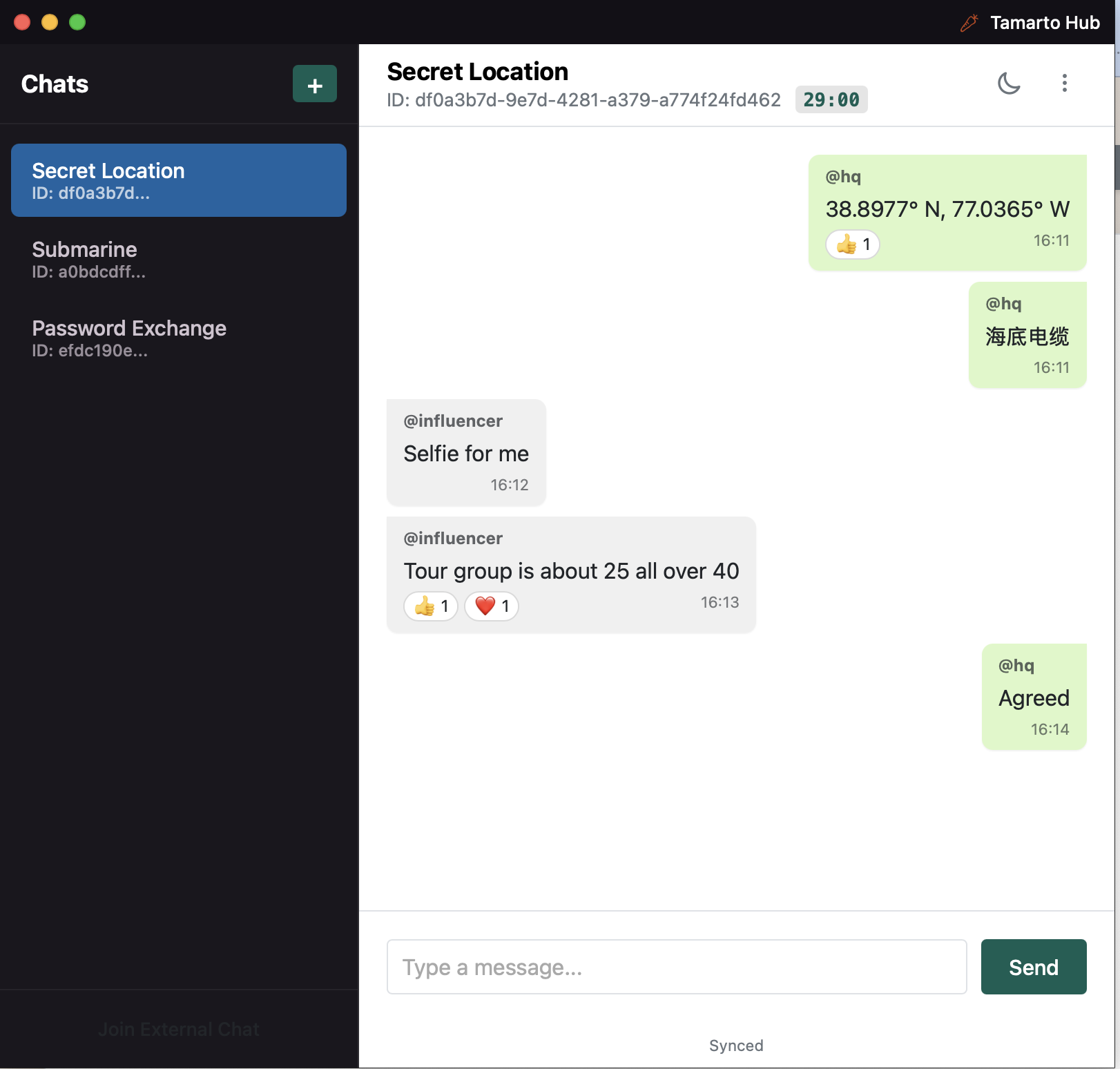
Tamarto is a decentralized platform where messages vanish by default. Data is encrypted via Argon2id + AES-256-GCM and segmented using overlapping redundancy, ensuring no single node ever holds the complete payload.